S3 Beauty, one of the biggest cosmetic online and physical retailers in Taiwan suffered multiple waves of brutal DDoS attacks on March 31st, 2020 which eventually took the service offline.
The website was overloaded by malicious requests and went offline almost instantaneously. They reached out to Mlytics for immediate managed DDoS protection assistance, and our customer success team and SOC team began the evaluation/onboarding process aiming to help S3 Beauty restore their service back online as soon as possible.
The total time for Mlytics to respond to S3 Beauty’s inquiry to have a fully-fledged managed DDoS protection service in action takes only 1.5 hours.
The first 30 minutes
The Mlytics customer success team quickly evaluated the requirements and immediately assisted S3 Beauty with the onboarding process with Mlytics’ SOC (security operation center).
Right away, we’ve discovered there were two main reasons why the security services they were using weren’t enough to fend off the attacks:
- The security services weren’t deployed globally, thus proven to be difficult to protect against attacks from other countries.
- Unable to differentiate between real users and malicious requests.
It’s imperative to understand that DDoS mitigation isn’t just about “blocking” attacks bluntly, it’s more “identifying” requests so that real users aren’t filtered out during the mitigation process.
The next 60 minutes: 93.5% malicious requests mitigated
In the first half of this phase, Mlytics has successfully mitigated the first wave of the DDoS attack and helped restore the service back online. The attacker immediately triggered a second and third wave which also didn’t take long for Mlytics to manage.
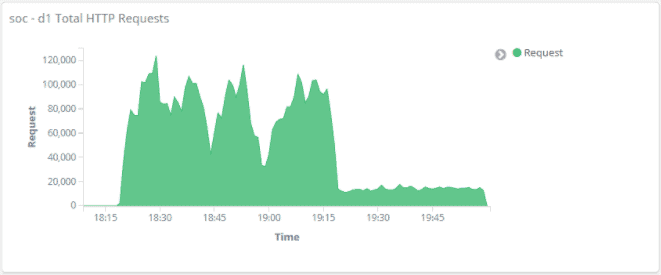
These series of attacks include layer 3, 4, and 7 DDoS attacks which can be difficult to mitigate against if without a sophisticated protection service in place. The key to mitigating complicated DDoS attacks like this within a short time is to employ the right tool and have access to intel to quickly “understand” the attack and take measures instantaneously.
Here are the traits we’ve observed from these attacks, and our strategy against them.
1st wave
Traits
- Requests flooding from China, Japan, the UK, and the US
- Most requests are from countries where S3 Beauty is not conducting business
Strategy
- Enabled challenge & response
- Redirect FQDN to the scrubbing center
- Geo block: Japan, US, UK, and China
2nd wave
Traits
- Multiple IPs found on single “user”
- Unusual referrers such as Baidu, Bing, Reddit, and QQ
Strategy
- Use X-Forwarded-For to identify the number of IP address
- Block requests from unusual referrers
The attacker cleverly forged search engine requests intending to evade the system. This method usually works if a service is using an average security service. Mlytics, however, uses its proprietary search engine verification technology, which can differentiate between forged requests and legit requests.
3rd wave
Traits
- Unusual query string activity
Strategy
- Continuous monitoring of the query string pattern
- Block unusual activity
The attacker is desperate at this stage and went back to the brute force method. The brute force method is extremely predictable and is filtered autonomously.
Key takeaway
A DDoS attack is extremely common on the internet. The most difficult part to deal with it is its unpredictability. It can go on forever or it can happen intermittently. Since there are many forms of DDoS attacks, it’s often difficult to fully prevent it from happening.
Subscribing to DDoS protection service is the logical decision to avoid businesses from exposing to the risk. But the important question is, what is a good DDoS protection service, and how to shop for one?
The answer is surprisingly simple: any service that can bring your service back to normal from DDoS hell in the shortest time is considered exceptional.
During a DDoS attack, real users may not even be able to access the service, which may cost businesses money, reputation, and more depending on how long the issue occurs. Thus, the faster the DDoS mitigation reaction time is, the fewer damage a business will have to stomach.
We’ve successfully demonstrated what a solid, effective, and flexible managed DDoS service looks like via S3 Beauty’s case and hoping to help more businesses to fend off malicious attacks in the future.
S3Beauty
Industry: eCommerce